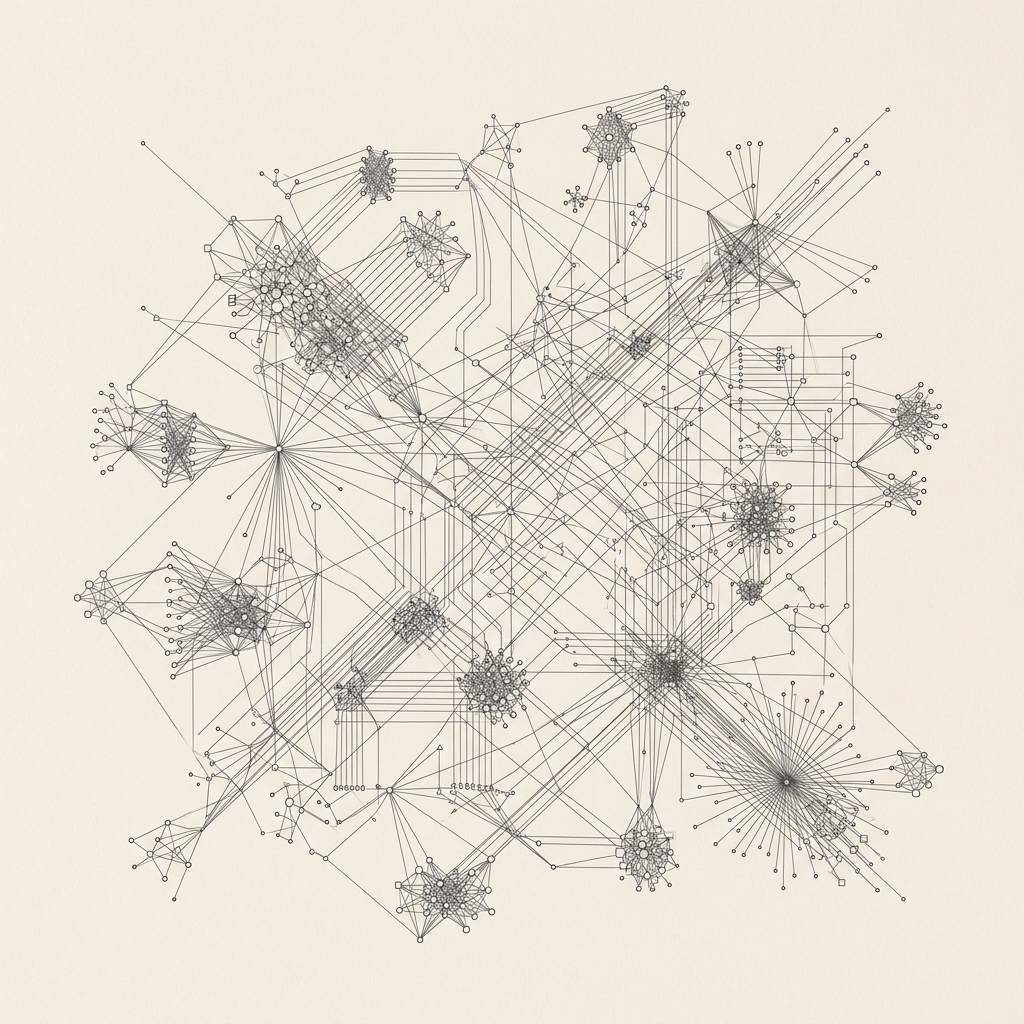
Large scale codebases are more than just collections of text: they are dense, multi dimensional networks of symbolic intent. Our latest research explores Symbol Centrality: the study of how autonomous systems can identify the hubs of an architecture to inform surgical interventions. This moves beyond standard retrieval augmented generation to a more structural understanding of intent, allowing an agent to "read the room" of a repository before initiating a task.
Beyond Traditional Retrieval Methodologies
Most retrieval systems rely on keyword relevance, which lacks the structural context required for deep refactoring. While keyword search can find a function name, it cannot tell an agent whether that function is a critical utility used by thousands of files or a minor helper in a peripheral module. Our research into structural reasoning utilizes an automated mapping methodology that identifies every symbol and relationship in the repository. The system distinguishes between utility components and architectural hubs: the central nodes where business logic is most dense.
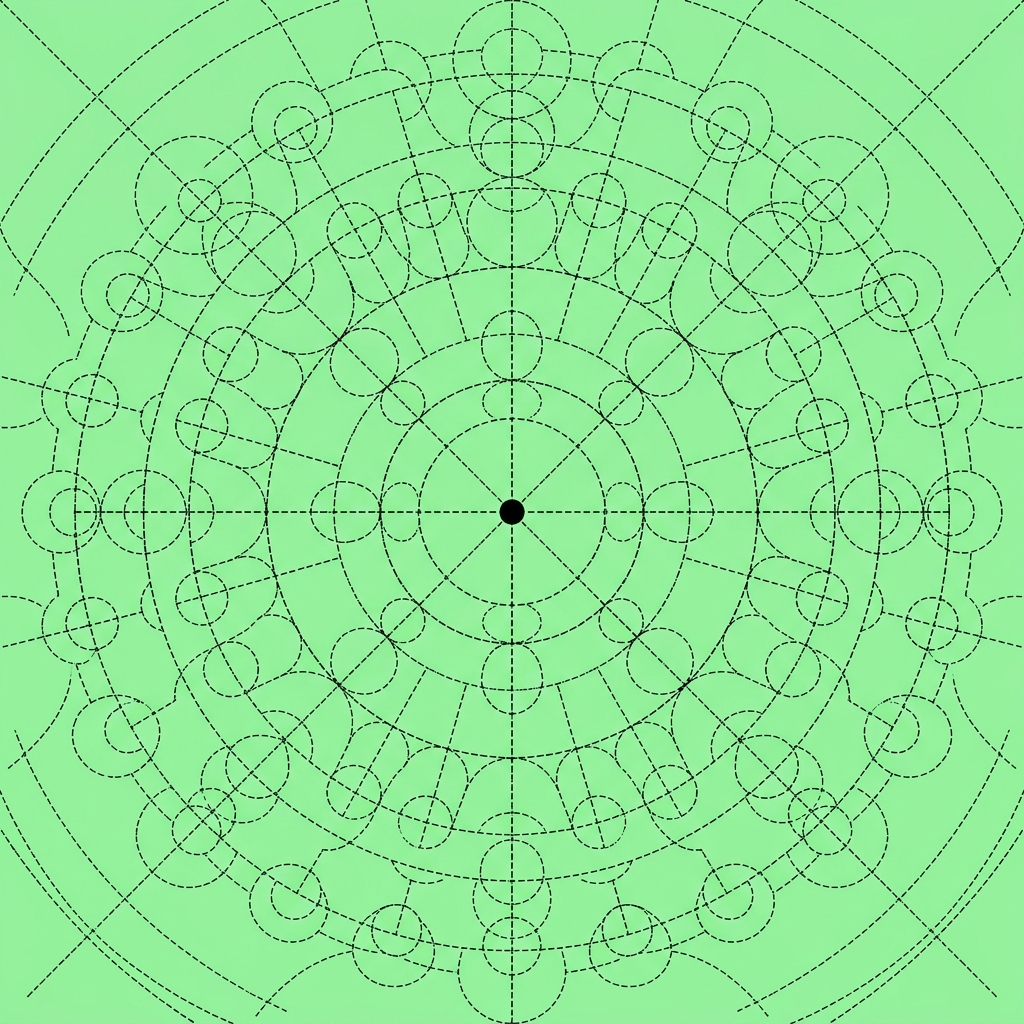
When the system initiates a task, it first synchronizes its internal representational state with the current structural state of the repository. By querying the semantic graph, the system can understand the blast radius of a potential change, identifying exactly which downstream dependencies will be affected before a single line of code is touched. This allows the system to establish a comprehensive situational awareness. In our testing, agents using centrality heuristics were able to find the root cause of a regression 50% faster than those relying on traditional text search.
Figure 2: Heatmap visualization of neural activation during semantic hub discovery. The graph identifies hubs by calculating the weight of inbound and outbound symbolic relationships.
Graph Construction and Pruning
The construction of the semantic graph is a continuous, background process. Our methodology involves extracting abstract syntax trees for every file in the workspace and linking them through a global symbol index. This is not a static index: it is a dynamic graph that updates in real time as the user or agent modifies the codebase. To manage the cognitive load on the agent, we implement sophisticated pruning heuristics. The graph helps the agent choose what not to read by identifying regions of the codebase that are structurally isolated from the current task scope.
This selective attention is critical for maintaining high reasoning depth. By focusing the agent’s discovery turns on the high centrality nodes relevant to the task, we ensure that the limited context window of the model is populated with the most valuable architectural evidence. This structural awareness allows CleanSlate to suggest refactors that are not just syntactically correct, but also architecturally sound, respecting the original design patterns of the project.
Intent Mapping and Architectural Safety
The semantic graph also enables Intent Mapping, where the system can identify if a requested change violates existing architectural philosophies. For example, if a proposed edit would introduce a circular dependency or violate a layer boundary, the graph reasoning layer can flag the issue during the planning phase. If a proposed edit to a central hub is identified as high risk, the methodology allows the system to suggest safer, more decoupled alternatives.
This provides a foundation for trust in safety critical engineering environments. The agent is no longer just a code generator: it is an architectural participant that understands the consequences of its actions. As we look toward the future, we are investigating ways to use this structural reasoning to perform "intent inference," where the agent can autonomously identify opportunities for architectural improvement without explicit user instruction.